Mastering Web Applications: A Journey from URLs to HTTP Handshakes
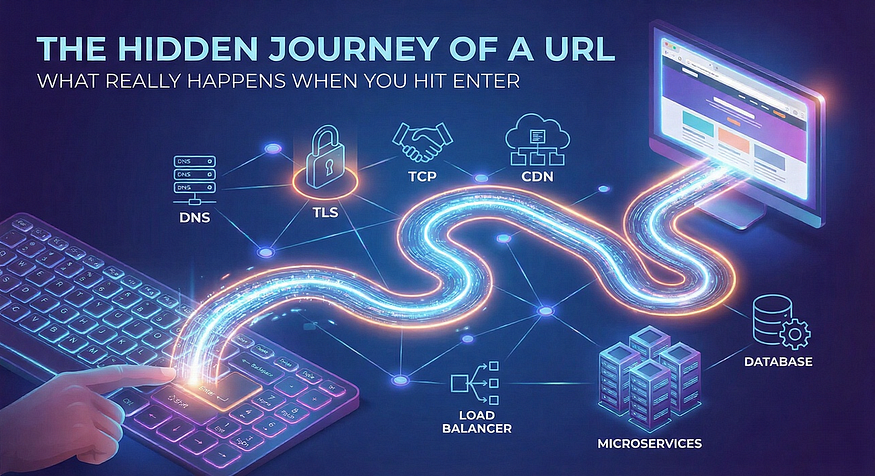
Welcome to the foundational journey of understanding how the web works! This writeup guides you through the TryHackMe “Web Application Basics” room, explaining the core components that power every website and application you use. Whether you’re a budding developer, a curious tech enthusiast, or an aspiring cybersecurity professional, grasping these concepts is the first crucial step.
We’ll break down what a web application is, decode the anatomy of a web address (URL), and dive deep into the language of the web itself: HTTP messages. Finally, we’ll put theory into practice with a hands-on task. Let’s begin!
🌐 Web Application Overview: The Planet Analogy
Think of a web application as a planet. What you see and interact with in your browser is just the surface. A vast, complex infrastructure exists underneath to make everything work.
- Front-End (The Surface): This is the user interface, built with:
- HTML: The skeleton and structure (like the planet’s simple organisms and their DNA).
- CSS: The styling, colors, and layout (the visual traits defined by that DNA).
- JavaScript: The logic and interactivity (the “brain” that makes decisions).
- Back-End (Under the Surface): The invisible engine includes:
- Web Server: Hosts and delivers the application’s content.
- Database: Stores and manages all data (like a planet’s library).
- Web Application Firewall (WAF): A protective layer that filters malicious traffic, much like an atmosphere blocking harmful rays.
Answers from the room:
- The component responsible for hosting content is the Web Server.
- The tool used to access web apps is a Web Browser.
- The protective security layer is a Web Application Firewall (WAF).
🔗 Uniform Resource Locator (URL): Your Web Address
A URL is more than just an address bar filler. It’s a precise set of instructions for your browser.
ComponentDescriptionExample / Security NoteSchemeThe protocol to use. HTTPS (secure) is always preferred over HTTP.https://Host/DomainThe website's name. Beware of typosquatting (e.g., g00gle.com), a common phishing tactic.tryhackme.comPortThe specific "door" to a service on the server. Defaults are 80 (HTTP) & 443 (HTTPS).:443PathThe location of a specific file or page on the server./room/webapplicationbasicsQuery StringExtra data sent to the server, starting with ?. Must be handled securely to prevent injection attacks.?search=helloFragmentA page section identifier, starting with #.#task-3
Answers from the room:
- The encrypted protocol is HTTPS.
- The practice of registering misspelled domains is typosquatting.
- The part for passing additional info is the Query String.
📨 HTTP Messages: The Conversation Protocol
Communication between your browser (client) and a server happens via HTTP messages. There are two types: Requests (what you send) and Responses (what you get back).
HTTP Request: Asking for Something
A request has a specific structure:
- Request Line: The opening statement (
METHOD /path HTTP/VERSION). - Headers: Metadata about the request (e.g.,
Host:,User-Agent:). - Empty Line: A critical separator between headers and body.
- Body: (Optional) Data sent to the server, like form inputs.
Key HTTP Methods:
- GET: Retrieves data. Should never be used for sensitive operations.
- POST: Sends data to create or update resources. Always validate this input!
- PUT/DELETE: Replaces or removes resources. Requires strict authorization checks.
- PATCH/HEAD/OPTIONS: Used for partial updates, fetching headers only, or discovering server capabilities.
Answer from the room: The mandatory separator that follows the headers is an Empty Line.
HTTP Response: The Server’s Reply
After processing your request, the server sends back a response with this structure:
- Status Line: Contains the HTTP Version, a Status Code, and a short reason phrase (e.g.,
HTTP/1.1 200 OK). - Headers: Server metadata (e.g.,
Content-Type:,Server:). - Empty Line: Separator.
- Body: The requested content (e.g., HTML, JSON, an image).
Understanding Status Codes:
- 1xx (Informational): “I’m working on it.”
- 2xx (Success): “Request fulfilled!” (
200 OKis the most common). - 3xx (Redirection): “Look over there for what you need.”
- 4xx (Client Error): “You made a mistake.” (
404 Not Foundis famous). - 5xx (Server Error): “I (the server) failed.”
Answer from the room: The message returned by the server is an HTTP Response.
Security Headers: The Silent Guardians
HTTP headers aren’t just for information; they are vital for security. Common security headers include:
Strict-Transport-Security (HSTS): Forces the browser to use HTTPS.Content-Security-Policy (CSP): Restricts where resources can be loaded from, blocking many cross-site scripting (XSS) attacks.X-Frame-Options: Prevents the page from being embedded in a frame (clickjacking protection).X-Content-Type-Options: Stops the browser from guessing file types, mitigating MIME-sniffing attacks.
🛠️ Practical Task: Making HTTP Requests
The room provides a built-in HTTP emulator to practice. Here’s the thought process for a typical task like “Make a POST request to update a user’s country and retrieve the flag”:
- Analyze the Objective: You need to change data, which requires a
POSTrequest to a specific endpoint (e.g.,/api/user/2). - Craft the Request:
- Request Line:
POST /api/user/2 HTTP/1.1 - Essential Headers:
Host: tryhackme.comContent-Type: application/x-www-form-urlencoded(specifies data format)Content-Length: [length of your body in bytes](must be accurate!)- Body: The data to update, e.g.,
country=US.
- Send and Observe: A successful update typically returns a
200 OKresponse with a confirmation message. - Retrieve the Flag: Sometimes the flag appears in the response body immediately. Other times, you may need a follow-up
GETrequest to the same endpoint to see the updated data containing the flag. - Mind the Details: Case sensitivity in methods (
POSTnotpost) and preciseContent-Lengthare often the keys to success.
By completing tasks like this, you move from passive theory to active understanding, seeing firsthand how the web’s fundamental protocol operates.
I hope this writeup has helped solidify your understanding of web application basics. If you’d like to dig deeper into any of these concepts, such as specific web vulnerabilities or more advanced HTTP features, feel free to ask
